Keylogging is typically done covertly through keyloggers(spyware) to gain access to your private information for malicious purposes. However, employers and parents might use this to monitor and safeguard their vested interests.
Keylogging or Keyboard capturing is performed through software programs (keyloggers) or hardware devices to track the activities of a keyboard.
While the programs themselves are legal, keyloggers are for stealing passwords and confidential information.
A keystroke recorder or keylogger can be software or hardware.
Keylogging software stores your keystrokes in a small file to be accessed later or automatically emails the information to the person monitoring your actions.
Some keyloggers are screen recorders also, as they capture your screen at random intervals.
How Does a Keylogger Get on Your Computer?
Anyone with access to your computer can install it as a virus or through some application installation. Therefore, make sure you download files from a trusted resource.
Decoding Keylogging
What is Keylogging?
According to Wikipedia-
Keystroke logging, often referred to as keylogging or keyboard capturing, is the action of recording (logging) the keys struck on a keyboard, typically covertly, so that a person using the keyboard is unaware that their actions are being monitored. Data can then be retrieved by the person operating the logging program.
Furthermore, it is a way to study human-computer interaction or keystroke dynamics through various techniques, ranging from hardware and software-based keyloggers to acoustic cryptanalysis.
Types of Keyloggers
Keyloggers are activity-monitoring programs that give access to every confidential data by logging every keyboard stroke. The software is installed on your computer and records everything you type. Then this log file is sent to a server, where cybercriminals can use this sensitive information for whatever purpose they desire.
There are Two Types of Keyloggers-
- Hardware– A Hardware keylogger is embedded inside your PC hardware. They also come as a plug placed between the CPU box and keyboard cable. In both cases, hardware has to be planted physically into your computer’s peripherals.
- Software– A software keylogger is a type of ‘malware’ installed to snoop into the keystrokes without impacting the computer. It is “good” malware, wherein it doesn’t harm its host.
Keylogger Software
A software keylogger is a computer program used to record inputs from the keyboard.
Remote- access software keyloggers communication happen by-
- Uploading the data to a FTP server, website, or database.
- Emailing data to a predefined email address.
- Transmitting data through an attached hardware system.
- Software enabling remote login to your local machine.
Some software keyloggers can capture additional information without any keyboard key presses. Like-
- Clipboard Logging – Anything copied to the clipboard is captured.
- Screen Logging – Randomly timed screenshots of your computer screen are logged.
- Control Text Capture – The Windows API allows for programs to request the text value of some controls, meaning that your password may be captured even if behind a password mask (the asterisks you see when you type your password into a form).
- Activity Tracking – Recording of folders, programs and windows opened and possibly screenshots of each.
- All search engine queries, instant message conversations, and FTP downloads with internet activities get recorded.
Keylogger Hardware
Hardware keyloggers monitor your activities without any software installations.
Some of the examples include:
- Keyboard Hardware – These loggers are a piece of hardware injected somewhere amidst the keyboard and the machine adjacent to the keyboard’s cable connection. This hardware keylogging is propitious because it is not reliant on any software, nor can it be recognized by any software.
- Wireless Keyboard Sniffers – It is possible for the signals sent from a wireless keyboard to its receiver to be intercepted by a wireless sniffer.
- Keyboard Overlays – Overlays are successful in ATM theft cases where criminals apprehend a user’s PIN by compounding in with the machine to go unrecognized.
Keylogging Attack Path
Keyloggers can intrude through attack tactics like phishing or social engineering, but they can also infiltrate through file-sharing sites via a software download.
How to Prevent Keylogging-Detection and Removal
Proactive protection is key to keeping your devices keylogger-free as prevention is always better than cure.
- Always read your terms of service before accepting them and investigate user feedback on the software you intend to install for helpful guidance.
- Ensure updated(against latest threats) security programs for all your networks. Select a security software that is familiar with every perceived keylogging invasion to expose it appropriately. These days most of the software automatically updates to shield against keylogger malware and other menaces.
- Malicious keylogging is injected mostly through software. Hence, install internet security software as an active shield on all your devices to safeguard against such infections.
- Never leave your mobile and computer devices unsupervised. If the perpetrator gets their hands on it, they may penetrate your private information, costing you a blunder.
- Criminals are using enticing ways to breach your confidential information. Do not use unfamiliar USB or external hard drives. Once plugged into your computer or mobile, they can infiltrate and begin logging.
Detection–
There are numerous keylogging detection methods, and none is a one-size-fits-all solution. Some of the below-mentioned tactics are known for successfully detecting keylogging.
- Start by running an antivirus to detect a keylogger on your system.
- Check your task list by pressing ctrl+alt+del in Windows to examine the tasks running. If you are unfamiliar with the result found, look them up on a search engine.
- Scan your hard disk for the most recent files stored. Look at the contents of any files that update often, as they might be logs.
- Use your system configuration utility to view which programs are loaded at computer start-up. You can access this list by typing “msconfig” into the run box.
Removal-
Taking responsibility for your personal computer’s security is the first step towards preventing a keylogger attack. Irresponsible use of a computer can put your data at risk.
- Always keep checking for unwanted software, and delete it.
- Don’t download files from unknown sources.
- While entering password information on banking sites, use a virtual keyboard.
- Use a password manager, as the manager will automatically enter the password, making keystrokes redundant (no keystroke, no keystroke logging). For households managing multiple accounts and devices, a reliable family password manager can further enhance security by generating strong credentials and securely sharing them without manual input.
- Use a next-gen powerful antivirus and internet security suite to safeguard your networks from advanced cyberattacks that can identify and remove malicious software as soon as detecting them.
Not Always Illegal
Some might think of keyloggers as illegal, but they do have legitimate and helpful applications. There are many legal use cases for installing a keylogger on computers.
For instance, keylogging helps IT departments troubleshoot problems and systems, and it helps them keep a tab on all employee activities to prevent a breach of confidential company data.
In addition, they are widely used to monitor children’s activity on computers- what they are doing offline and online.
Also, these programs can monitor your computer activity when you are away from it if someone has access to it.
Legal Aspect-
If you install a keylogger on a device you own, it is legal. If a keylogger is installed behind the owner to steal data, it is illegal.
Keystroke monitoring for privileged users can be a vital step in adhering to compliance standards and ordinances.
How to Install a Keylogger in Total Stealth
Disable the antivirus program during the installation-
- Delete the installation file after finishing setup.
- After installation, enable the antivirus and perform a scan. Choose Allow/Trust (do not block it or move it into Quarantine).
- Enable monitoring and if the antivirus will detect anything, choose again Allow/Trust (do not block it or move it into Quarantine).
- Set a password to prevent unauthorized modifications of keylogging settings.
What is Keylogging Software?
These are invisible software programs inside a computer, don’t have icons on the desktop, don’t appear in program files, task manager, uninstall programs etc.
They record all keywords typed on that computer.
Keylogging software can preserve all keystrokes, including username and passwords, to save a history of visited websites, applications started and used, to save screenshots (captures of the entire screen) at fixed intervals.
Recorded data is automatically sent to a precise email address or server to the person who installed it, and has access to view remotely the activity and keywords typed on that computer.
What to Look for in Keylogging Application
Keylogging Features-
- Visual and textual evidence exists for every keystroke and copy/paste operation.
- Create anti-logging rules, when keystrokes won’t be recorded when the user is checking their personal bank account or entering a credit card number.
- Configure behavior rules that alert or lock out a user when specific keystrokes are pressed in certain applications.
- Full recording of invisible and hidden characters.
Besides recording keystrokes, look at the following keylogging aspects:
Monitoring Features– In addition to capturing screens, the best keyloggers track the webcam, record the microphone, clipboard (the content of copy-paste), and track document changes, names of documents sent to the printer, all addresses of visited websites and programs used.
Reporting & Delivery– Best keylogging devices provide advanced filters, search functions, built-in reports, and custom ones. These reports are automatically sent by email to the person who installed these programs for monitoring in an online account.
User Behavior Analytics– If you are monitoring your children or employees, you should be able to block the access to different websites (social networks, adult) and programs (games, messengers). You can set the monitoring program to start at certain events or keyword typed and protect the access to the interface with a password.
Invisibility/Stealth– A keylogger should stay hidden, this means that the user should not see any entry or record related to the program on Desktop, Start Menu, Add/Remove Programs etc. Also it must stay undetectable by antivirus programs – if it is detected by antivirus, the user can block it and the monitoring activity will not work.
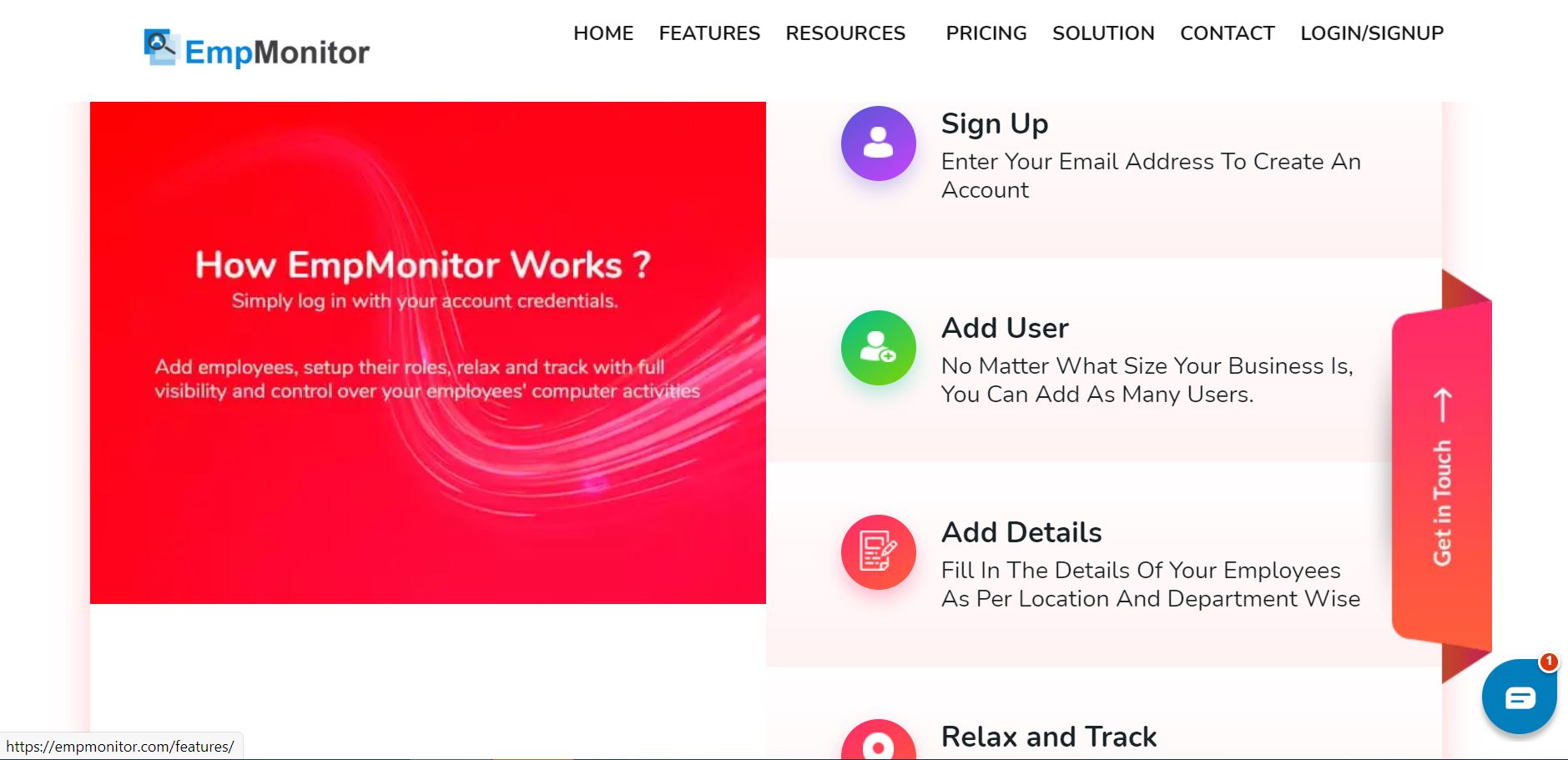
EmpMonitor is one such leading keylogging application that is breaking new grounds with its advanced user behavior analytics software to assist employers gain insight into their employees’ daily activity, demeanor, professionalism, and productivity.
EmpMonitor is a renowned software for employee management and productivity tracking of the workforce. Its cloud implementation solution can track keystrokes without physical access to the user’s desktop.
Empmonitor’s keystroke monitoring integrates seamlessly with the other robust features of the software, including user behavior analytics, internet, and instant message activity tracking.
It is a surveillance software to track, capture, record, and log all keyboard activity by a user or employee whether into web browsers, instant messages, Emails, applications, documents, and programs.
Included with EmpMonitor’s tracking features is a wide range of insight for management about their employees, from if they are using unprofessional language to if they are repeating easy to guess passwords across all their accounts.
Whether monitoring remote or on-site users, employers have complete insight into all keystrokes and copy/paste actions.
EmpMonitor is an intelligent software to protect a company from insider threats with its unique stealth mode feature.
Key Features-
- Monitors Employees: EmpMonitor captures and records the productivity of every team member working remotely.
- Secure: It is a safe and secure tool that blocks all kinds of insider threats. This tool reviews, records and analyzes threats from time to time.
- Enhanced Productivity: EmpMonitor boosts up your productivity levels by eliminating the rest hours and idle activities.
- Time Management: It tracks the remote team’s working and non-working hours, making it the best choice for remote teams management tools.
- Chat Monitoring: EmpMonitor tracks the amount of time spent by employees on chat applications during their work hours.
- Clients Feature: EmpMonitor also monitors time spent on a client and client’s project.
- Powerful Reports: EmpMonitor provides clean and detailed reports and graphs showing your staff’s performance and productivity.
- Web & Apps Usage Monitoring: EmpMonitor also tracks the most visited website URLs and Applications to help you track your staff members if they are using more time on social media during office hours.
- Payments: EmpMonitor automates all the payroll processes and payments with the clients too. It also automates the billing process.
- All Devices: EmpMonitor is a cross-platform tool and is compatible with all devices and operating systems like Windows laptops, MACs, Android Devices, etc.
- Integrations: EmpMonitor can be easily integrated with other popular accounting and managing tools to extend tool functionality, making it a better choice for productivity measuring tools.
- Alerts: EmpMonitor provides regular alerts to help you prevent time wasting activities and increase productivity at the remote workspace.
- GPS Tracking: EmpMonitor also tracks the exact location of your remote team members via their device and lets you know from where they are working.
- Off Track Reminders: EmpMonitor also alerts you to stay away from non-work websites during work time to achieve maximum productivity.
- IP Safelisting: EmpMonitor also safelists IP addresses and allows team leaders to visit specific websites via white-labeled IPs.
- Attendance Logs: EmpMonitor also keeps a record of your remote team members’ exact login and logout time for the last seven days.
- Track Breaks: It also tracks the total amount of time spent away from the working devices.
- Keystrokes: EmpMonitor also tracks the keys pressed by your remote team members while working in real-time.
- Browser History: This tool keeps the device history of your team members safely on the cloud even if your remote team members clear their device history at their end.
Sign Up to EmpMonitor is also easy, start tracking by creating an email account absolutely free for a 15 days trial for 5 users.
Latest Posts-
Behavior Analytics- Top Applications 2022
Productivity- Definition, Considerations, Some Tips & More
12 Reasons of Using Employee Time Calculator in Your Organization
Word of Advice-
- Using a complete internet security solution is the best defense against keylogging malware.
- We recommend consulting cyber law experts before installing any monitoring(keyloggers) programs for surveillance purposes.
- Install keylogging monitoring only on computer networks you own, or you have authorization/ administrative rights.