HR forensics is becoming increasingly critical as employment tribunals across major cities report a sharp rise in cases involving digital records in 2023. For many decisions, emails, chat logs, and system activity were central. Yet many HR teams still lack a structured approach to collecting and presenting this data. As a result, legal losses, reputational damage, and unnecessary settlement costs could have been avoided.
Workplace legal disputes are no longer decided by verbal testimony alone. Digital timelines now play a crucial role. A missing email chain or incomplete access log can shift the outcome of a dispute. This is where forensic investigation becomes critical. It ensures that digital evidence is collected, preserved, and presented in a legally defensible way.
Organizations face significant risk without proper forensic investigation. Poorly handled data may expose them to privacy violations, which creates an even worse scenario. HR leaders must now think like investigators, not just administrators.
Hit ‘Play’ Button & Tune Into The Blog!
What Is HR Forensic Investigating?
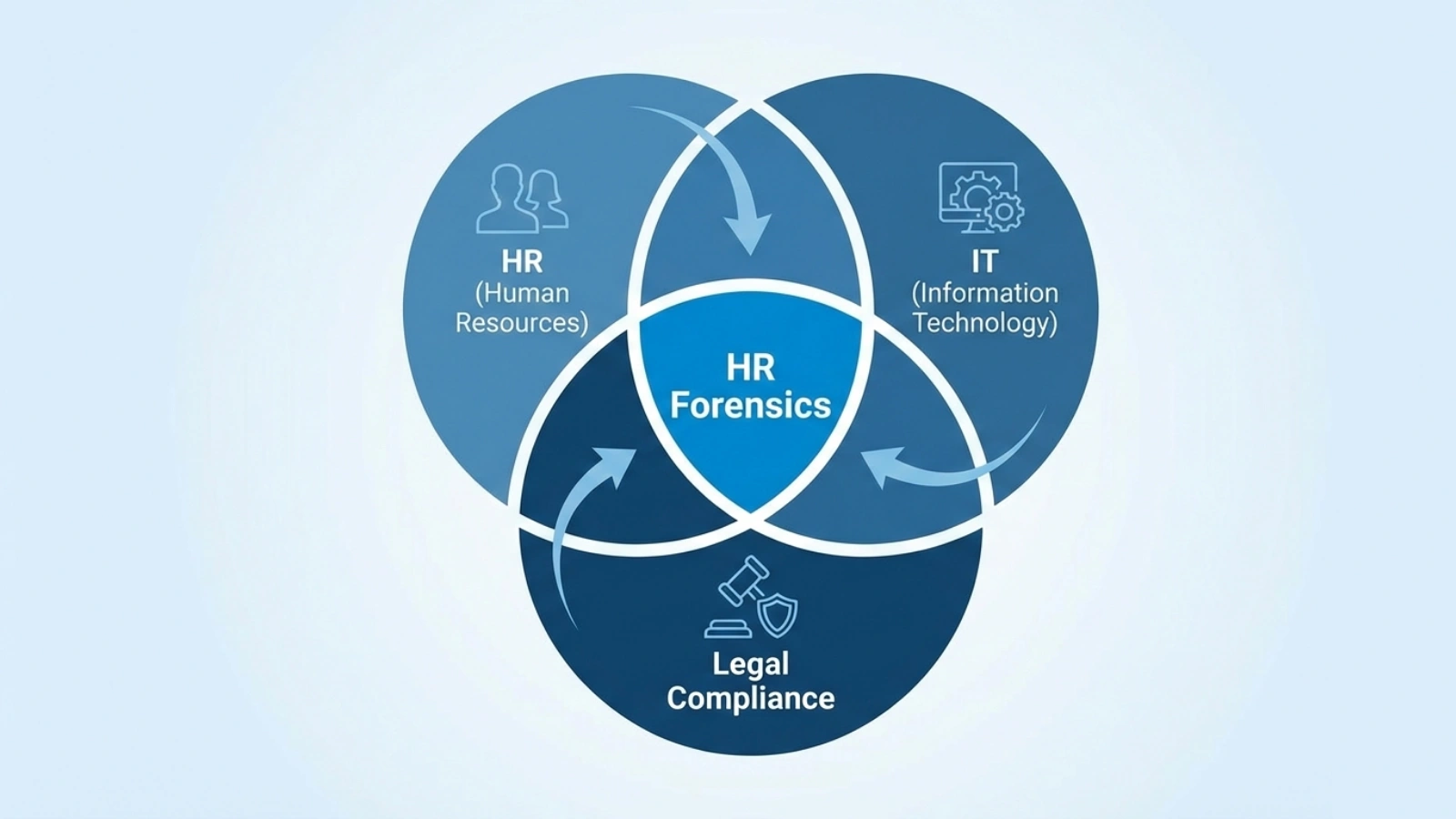
HR forensics investigations are a systematic process for collecting and analyzing electronic evidence of employee actions in the workplace. It involves combining human resources with legal compliance while using technical methods to validate digital evidence. The collected data is used to establish objective proof of what occurred, based on electronic records that can be verified.
In today’s workplaces, almost every activity creates a digital record. Email provides insight into intent, chat logs reflect how conversations unfolded, and access logs show who was present at specific times. File histories enable tracing changes made to documents. A successful forensic investigation connects these pieces of digital evidence into a coherent narrative.
This discipline sits at the intersection of HR, IT, and legal departments. HR identifies the issue. IT secures and extracts relevant data. Legal teams ensure compliance with regulations. Coordinated investigative efforts protect both employee rights and organizational interests.
Workplace data sources commonly used include:
- Email communications
- Messaging platform logs
- System access records
- Time tracking data
- Screen activity captures
- File transfer histories
Every source must be verified. A comprehensive forensic examination validates timestamps, metadata, and user attribution. These measures prevent claims of manipulation.
Technology plays a pivotal role here. Employee monitoring software like EmpMonitor assists in maintaining detailed activity records. When policies are transparent, these systems support compliant investigation processes without appearing intrusive. The key is governance, not surveillance.
Common Employment Tribunal Scenarios
Employment disputes are often resolved based on digital evidence. Below are five common scenarios where structured forensic investigation proves decisive.
1. Wrongful Termination Claims
If an employee claims dismissal was unjustified, digital performance records, attendance logs, and documented warnings can clarify events. Through HR forensics investigation, HR can present objective timelines that support or challenge allegations.
2. Sexual Harassment Cases
Harassment allegations frequently involve messaging platforms. Screenshots alone are insufficient to establish conclusions. A defensible investigation process retrieves complete chat histories with verified timestamps. This ensures context is not distorted.
3. Time Theft and Productivity Disputes
Remote work has increased productivity disputes and time thefts. Activity logs, login records, and application usage reports become critical. Structured forensic investigation confirms whether contractual obligations were met.
4. Data Breach Incidents
Insider threats can lead to data breach. File access histories and transfer logs reveal unusual activity patterns. A proper investigation identifies responsible accounts while preserving evidence integrity.
5. Discrimination Lawsuits
Claims of biased treatment may hinge on comparative records. Promotion timelines, performance evaluations, and communication trails provide insight. Objective forensic investigation minimizes reliance on subjective interpretations.
In each scenario, evidence must be organized, authenticated, and clearly documented. Emotional arguments rarely prevail over verified digital facts.
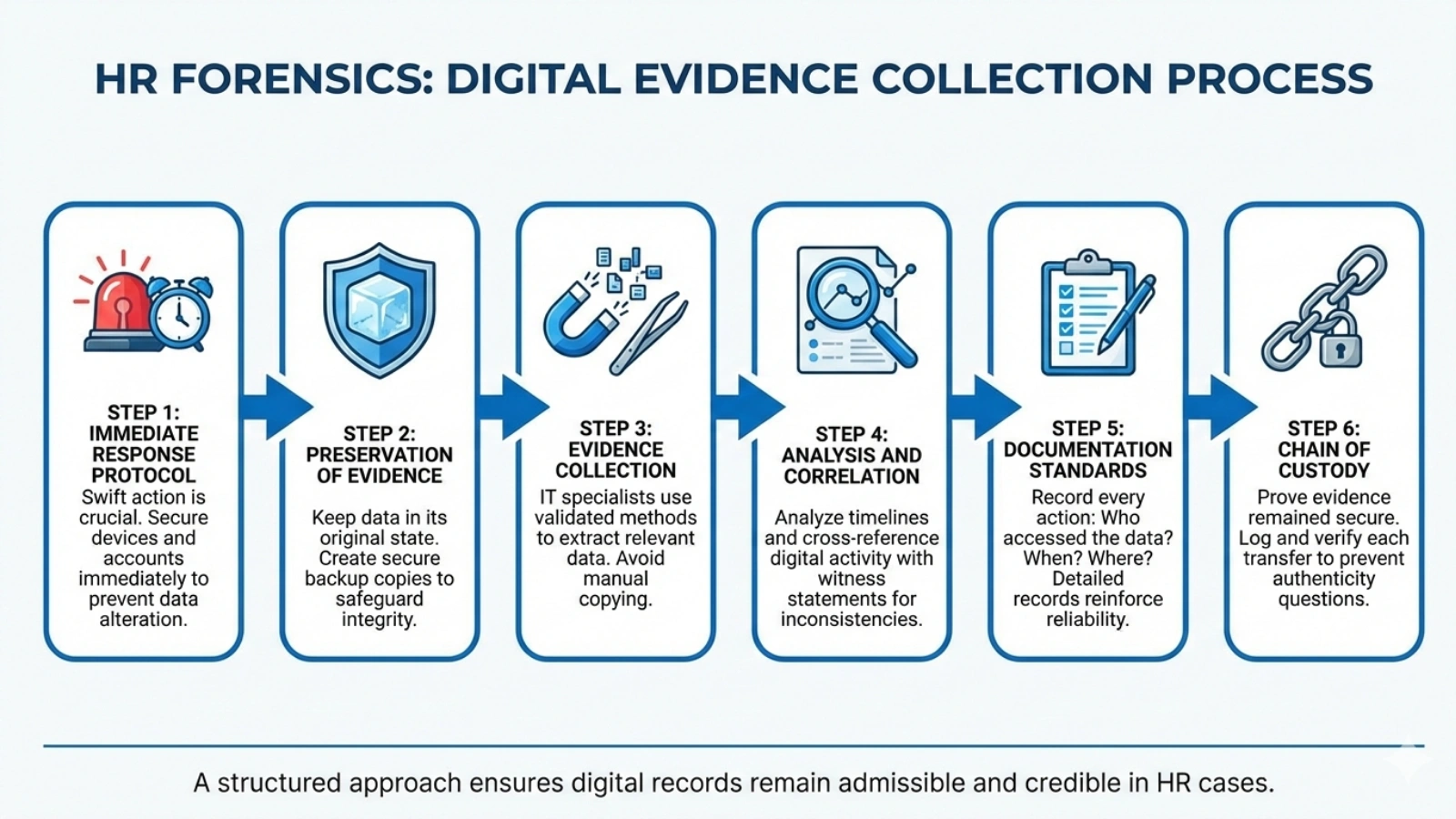
The Digital Evidence Collection Process
A structured approach ensures digital records remain admissible and credible. Below is a step-by-step framework for effective forensic investigation in HR cases.
Step 1: Immediate Response Protocol
Once a complaint arises, action must be swift. Relevant devices and accounts should be secured immediately. Delays increase the risk of data alteration. Early containment is fundamental to an effective investigative response.
Step 2: Preservation of Evidence
Data must be preserved in its original state. This includes emails, system logs, and cloud records. Backup copies should be created securely. Preservation safeguards the integrity of the forensic investigation process.
Step 3: Evidence Collection
IT specialists extract relevant data using validated methods. Random copying or manual downloads may compromise metadata. Technical precision strengthens overall credibility.
Step 4: Analysis and Correlation
Investigators analyze timelines and cross-reference digital activity with witness statements. Patterns often reveal inconsistencies. Thorough analysis elevates the value of forensic investigation beyond surface-level review.
Step 5: Documentation Standards
Every action must be recorded. Who accessed the data? When was it stored? Where is it kept? Detailed documentation reinforces the reliability of the investigation framework.
Step 6: Chain of Custody
Chain of custody proves that the evidence remained secure. Each transfer is logged and verified. Without this record, tribunals may question authenticity. Proper chain management is central to professional forensic investigation.
Organizations that prepare these protocols in advance respond more effectively. Tools like EmpMonitor simplify historical data retrieval. Structured logging ensures that the investigation process can begin immediately when disputes arise.
Legal Admissibility Requirements
Digital evidence must meet specific legal standards. Authentication is the first requirement. Employers must prove that records are genuine and unaltered. A disciplined forensic investigation approach establishes authenticity through metadata validation.
Privacy compliance is equally important. Regulations such as GDPR and state-level privacy laws restrict how employee data may be collected and used. Transparent policies are essential before initiating an investigation.
Employee notification requirements also vary by jurisdiction. Monitoring policies must be clearly communicated. Failure to disclose monitoring may weaken a legal defense.
Presentation style matters in tribunals. Evidence should be organized chronologically and explained clearly. Complex technical jargon should be avoided. A structured investigation report makes findings understandable for non-technical decision-makers.
Technology Tools for HR Forensics
Technology simplifies evidence readiness. Manual methods are risky and inefficient. Integrated tools enhance accuracy and consistency in forensic investigation.
Employee Monitoring Software
Monitoring platforms track application usage, login times, and productivity trends. EmpMonitor offers centralized dashboards and secure reporting features. These capabilities support ongoing compliance and structured investigation.
In addition, EmpMonitor provides real-time activity tracking with detailed application and website usage reports. HR teams can view productivity summaries, idle time analysis, and attendance records from a single interface. The platform also includes optional screenshot capture for visual context during disputes.
Comprehensive timesheets and automated attendance logs help verify work hours with accuracy. Role-based access controls ensure sensitive data remains protected during investigative reviews. With historical data retention and exportable reports, EmpMonitor makes it easier to retrieve defensible digital records when formal workplace investigations arise.
Email Archiving Systems
Automated email archiving prevents deletion and loss. Archived communications strengthen investigations by ensuring historical completeness.
Access Log Analysis
System access records reveal unusual login behavior. Integrated analysis tools accelerate forensic investigation in breach or misconduct cases.
Screen Recording Evidence
Visual records can clarify disputed actions. When implemented ethically, they support contextual reviews without excessive intrusion.
Time Tracking Forensics
Attendance logs confirm work patterns and contract adherence. Accurate time data strengthens investigations in productivity disputes.
The right tools reduce manual errors. They also create structured documentation that tribunals value.
Case Study: A Tribunal Win Through Digital Evidence
A mid-sized technology firm faced a wrongful termination claim. The employee alleged discriminatory dismissal. Initial internal reviews were inconclusive. However, structured forensic investigation revealed consistent performance warnings and documented communication trails.
Activity logs showed repeated policy violations. Email archives confirmed formal notices were issued. Chain-of-custody documentation proved the records were authentic. The tribunal ruled in favor of the employer.
The company avoided a settlement exceeding $250,000. More importantly, its reputation remained intact. This outcome was possible because the investigation was systematic, not reactive.
Building Your HR Forensics Capability
HR Forensics investigation should be treated as a core competency within organizations. Training HR teams on evidence handling reduces procedural errors. Collaboration with IT ensures technical precision.
Clearly defined policies determine when investigations begin and how data is accessed. Regular audits test system readiness. Platforms like EmpMonitor provide consistent recordkeeping that strengthens long-term preparedness.
External forensic experts may be necessary for complex cases. However, internal readiness reduces dependency and accelerates response times.
The Future of HR Forensics
Workplaces are becoming increasingly digital and remote. Artificial intelligence tools are now helping with anomaly detection. Predictive analytics may soon highlight risks before conflicts escalate.
At the same time, privacy regulations are tightening. Organizations must balance transparency with compliance. The future of forensic investigation lies in proactive governance, not reactive damage control.
Companies that invest in structured systems today will face fewer surprises tomorrow.
Also Read!
Prevent Source Code Theft: Protect Your IP From Developers
Is It Legal To Monitor WFH Employees? A Global Compliance Guide
Take the Next Step
Workplace disputes are inevitable, but preparation makes the difference. Assess your organization’s readiness for digital evidence handling. Request a demo of EmpMonitor to explore structured monitoring and reporting features. Download a forensic investigation checklist to evaluate current policies and identify improvement areas.
FAQs
How long should companies retain digital logs for potential disputes?
Retention periods vary by jurisdiction. Many employers align log retention with statutory limitation periods for employment claims.
Can deleted emails be legally recovered during investigations?
Yes, deleted emails can often be retrieved if backups or archives exist. Recovery must comply with privacy regulations and documented evidence procedures.
Does forensic investigation apply to small businesses?
Absolutely. Smaller organizations face similar tribunal risks and benefit from structured evidence handling.
Are remote employee devices subject to workplace investigations?
Policies determine scope. Clear agreements must define monitoring boundaries for remote environments.
When should external digital forensic experts be engaged?
External digital forensic experts should be engaged in cases involving complex data breaches, large datasets, or cross-border legal issues that require specialized expertise.