Refining Excellence Together
Our Valuable Clients & Resellers
Across The Globe
Our Valuable Clients & Resellers
Across The Globe
Echoes of Satisfaction
The Heart of Our Journey
The Heart of Our Journey
Our Product Suite
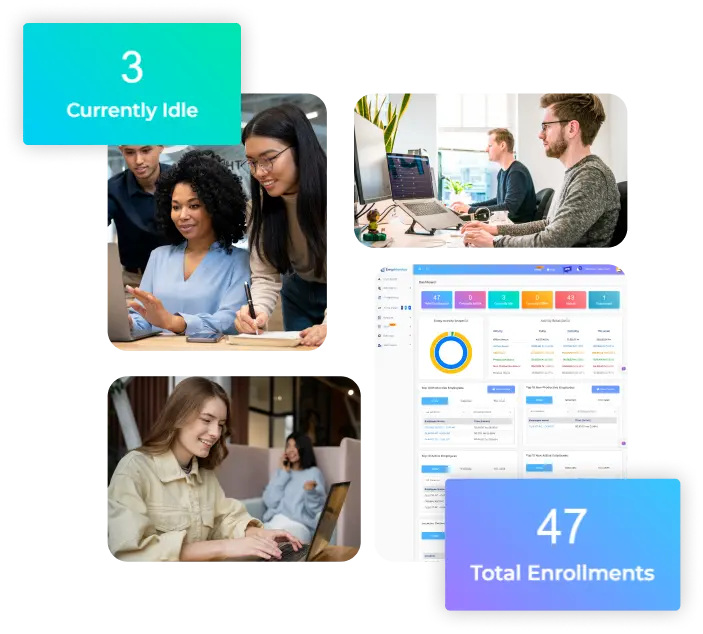
Stop guessing. Start seeing what your team actually does.
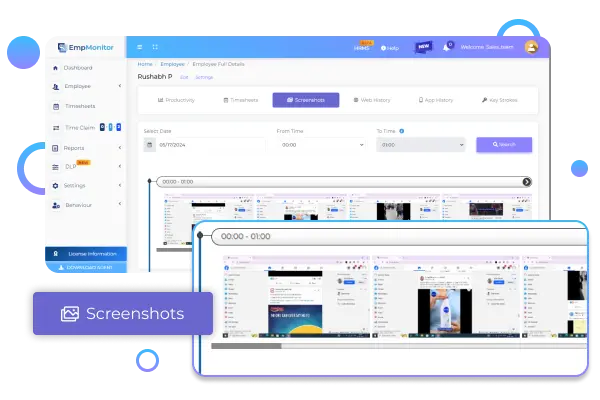
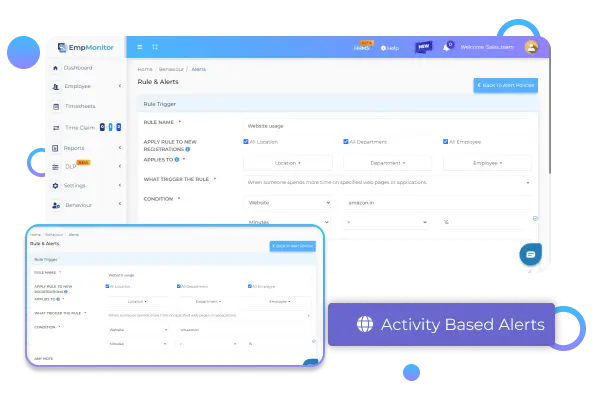
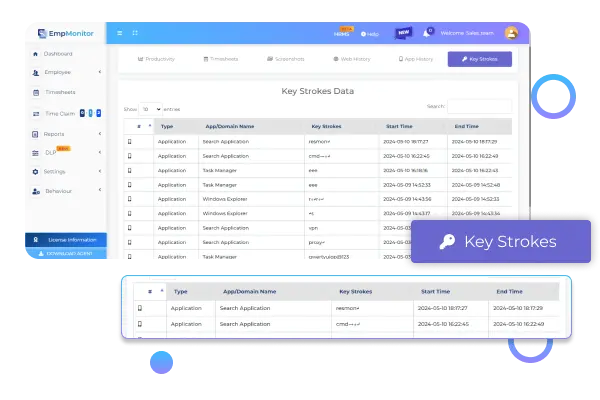
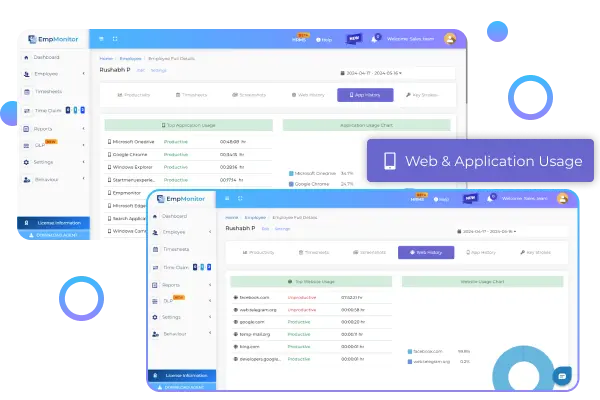
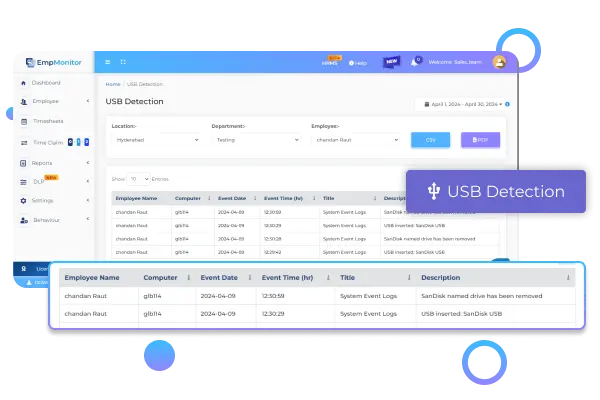
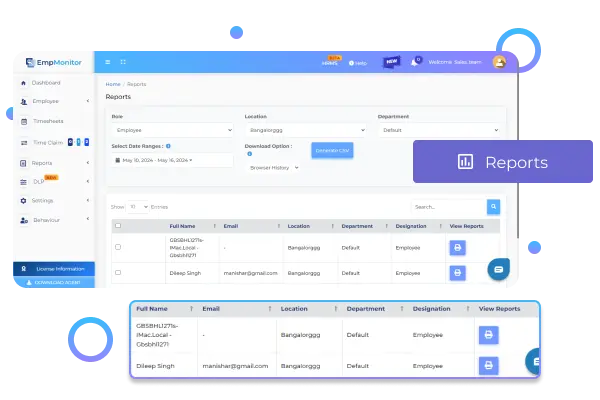
Features That Power
EmpMonitor
Unleash a suite of monitoring solutions to manage your workforce more effectively and in a more informed manner
Data-rich Insights
Give Your Enterprise
Our The EmpMonitor Advantage
Give Your Enterprise
Our The EmpMonitor Advantage
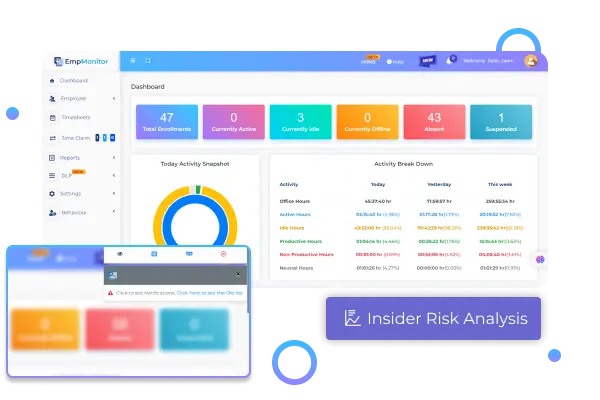
Enhanced Security
Enhanced Security
Get started with refined & best workforce management software that ensures high levels of security and protects your business from menaces.
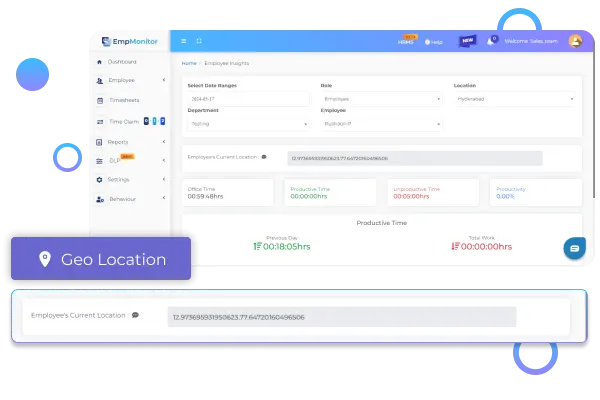
Behaviour Analysis
Behaviour Analysis
Achieve organizational goals by identifying the optimal pattern of employee behavior and implementing it in other business operations.
Optimal Productivity
Optimal Productivity
Take your employee’s focus to a more concentrated workflow by minimizing distractions and leading them to enhanced productivity.
Trusted by HR leaders & business owners
Discover Information
Frequently Asked Questions