The hard and factual proof
In 2020, an estimated 54% of organizations switched to remote work in response to the covid-19 pandemic.
2020 – 30% increase in data breach cases (5% involving insider aid)
By May 2020, a 30% increase in data breach cases was observed, with about 5% of these cases involving insider aid.
2020 – 1,001 confirmed data breaches in the US alone
According to one report, 2020 has seen 1,001 confirmed data breaches in the US alone.
What these numbers mean for your business
Criminals do not discriminate between company sizes.
The 9,780,931 data breaches mentioned above are spread across businesses of all shapes, sizes and industries. Many of these businesses look and operate exactly like yours.
And none of them ever believed it would happen to them.
Maybe:
- You trust your team.
- You have excellent KYE and hiring procedures.
- You’re confident that nobody would want to infiltrate your company and steal your data.
But is it really worth the risk?
A data breach opens you up to all sorts of damages
The most obvious and immediate outcome of a data breach is loss of competitive advantage and market share. If your data falls into the hands of a competitor, they could use it to steal your customers or sabotage your operation.
But that’s not the only threat you need to worry about.
Businesses that fail to protect their customers’ data as per GDPR regulations are mercilessly hit with massive fines up to ten million euros.
Here’s a direct quote from the General Data Protection Regulation (GDPR) document:
Frequently Asked Questions
Here are some frequently asked questions that you might be thinking about.
Is EmpMonitor right for your business?
You and your business are unique, and so are your needs.
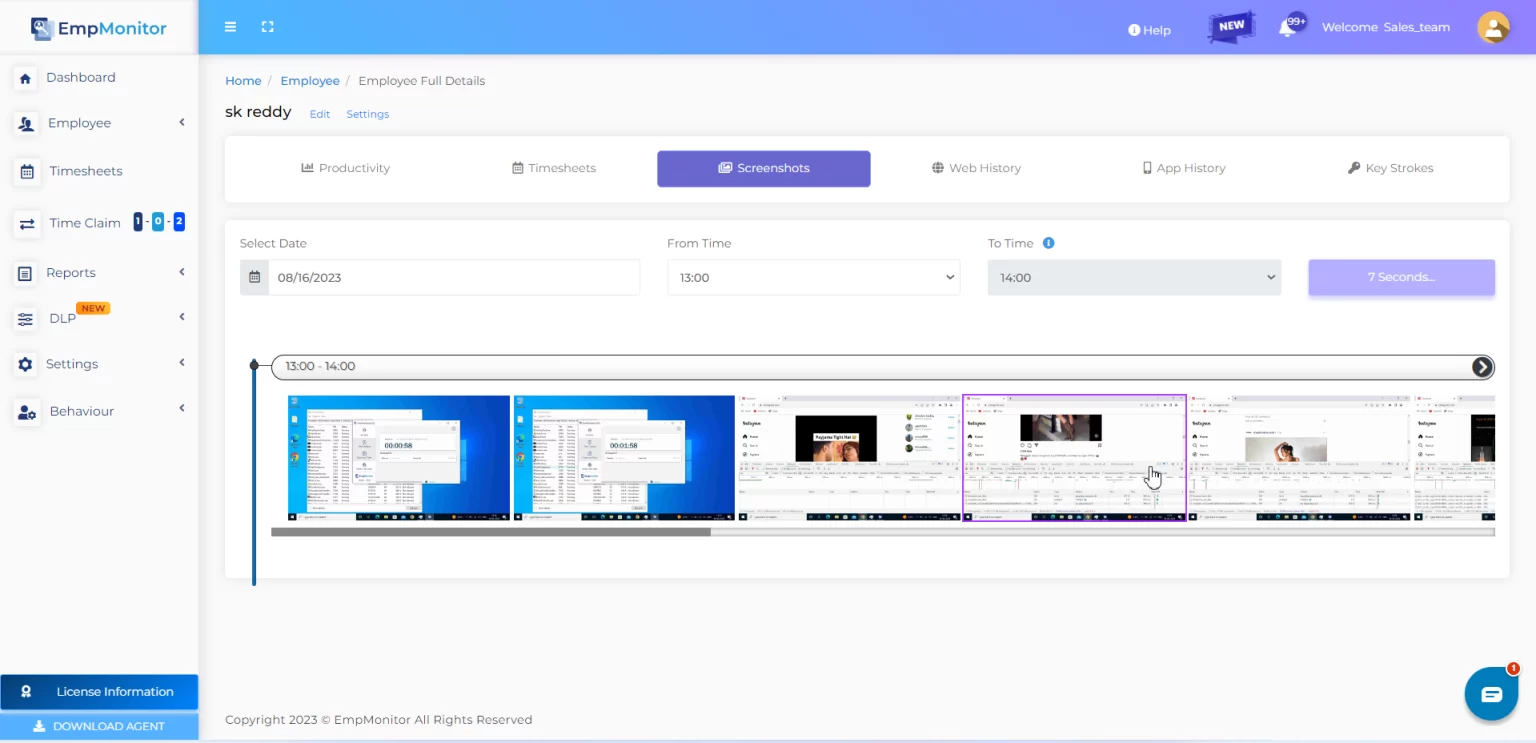
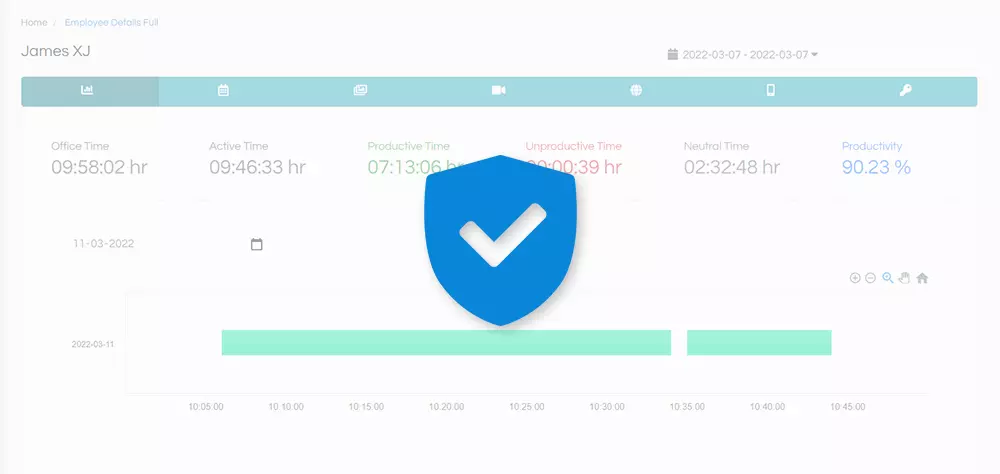
EmpMonitor doesn’t dictate how you work. Quite the contrary—YOU dictate how EmpMonitor should serve you. EmpMonitor works with you and for you, providing you precisely the information you want—no more, no less—so you can make the best decisions for your business without any distractions. With EmpMonitor, the tool is your servant, not the other way around.
“If you can’t measure it, you can’t improve it.” – Peter Drucker
If you want to:
Then the answer is:
YES, EmpMonitor is right for your business.
Businesses from all industries and verticals are using EmpMonitor to become more cost-effective and profitable every day.
Client’s Testimonials
Ellsworth B. Ambrose
File Review Manager
“EmpMonitor has provided a complete monitoring package for our business, and it really helped us prevent data loss in our business. Thanks to this we have been able to analyze employee behavior to avoid any kind of anomalies in our business. Especially, I find it a great tool for small and medium-sized enterprises like ours.”
Kristian
Startup Founder
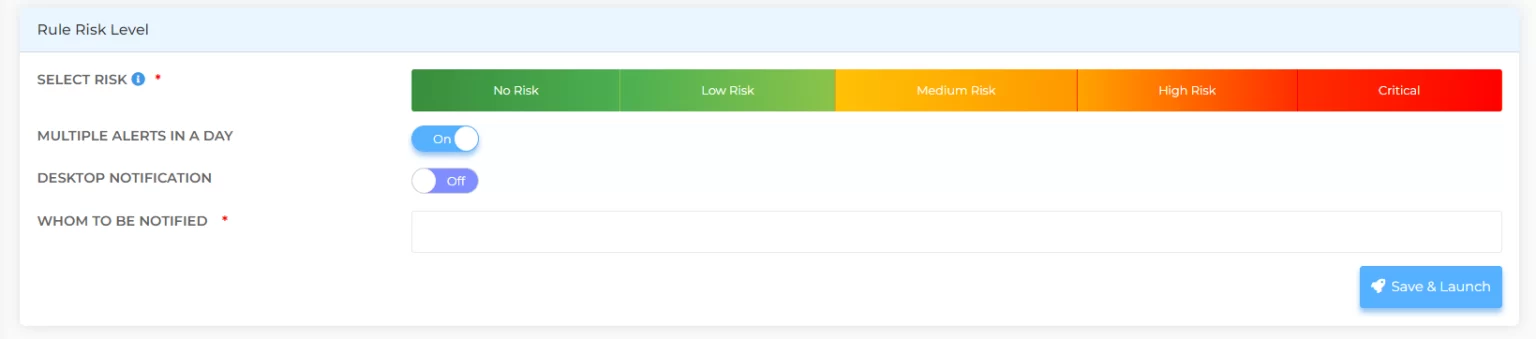
“We have been quite impressed with this software. It has all the mature features that we need to manage our workplace. With an easy-to-use dashboard, it becomes feasible to keep track of the work time and productivity of employees. Thanks to the pre-alert system, which notifies us ahead of time before any mishaps.”
Rita J. Frink
Startup Founder
“After testing out 8 of the best software in the market in a row, I finally found the one that offered robust monitoring along with every feature that one could ever ask for. And when I say every feature, I mean it. EmpMonitor is hands down the best. Period.”
Bradley Helms
“Recently, I purchased and installed the recent version of your software after a recommendation from one of my co-workers, and I am already so impressed with it! Very organized interface, easy operation, and accurate results. I would happily recommend it to everyone.”
1solutions
“The company has seen considerable benefits in their employee’s productivity by integrating EmpMonitor with other tools in their workplace.”
Lexmores
“EmpMonitor puts an end to data security concerns and helps them to reduce the suspicious activities at their premises.”
James Cooper
Digital Specialist
“Installed and upgraded to the latest version on a friend’s recommendation and found to be most versatile with the systematic interface, easy operation, and accurate results. Would highly recommend it to all business owners.”
Patrick Lambert
Business Manager
“EmpMonitor is a solid employee monitoring and analytics solution that is laser-focused on worker productivity, with attractive pricing and an easy-to-use user interface. This is a valuable tool to keep an eye on during the COVID-19 pandemic and further.”
Jonathan Matthews
Operations Lead
“EmpMonitor has been of great use for us. Our employees have shown higher levels of productivity, and we have been able to keep up to date with tasks. During remote work, our output has not reduced, and our workforce is still as engaging as ever.”
Patrick Buchanan
Staff Manager
“Our firm had some complications regarding the optimization of output. We also wanted a deeper understanding of how our employees are spending time and dividing their work. EmpMonitor not only helped us to access insights into their workings but it also helped our employees to self-evaluate and use better time management practices on their own.”
Amar Singh
Team Lead (Web Design)
“EmpMonitor has provided us with great tools to not only manage but optimize our media designing works. It helped us increase the pace at which we were putting out creatives and videos on a working day.”
Ashis Junanker
Marketing and Advertising
“Impressive functionality! Empmonitor has been really useful with productivity management and ensuring data security in our business. Thanks to this we have found a few work negligence which was fixed right on time before causing any damage. The best employee monitoring option, certainly.”
Dedicated apps for all your favorite platforms
EmpMonitor allows you to access your data anytime, anywhere, and from your favorite platforms thanks to dedicated apps for most popular platforms.
Each app is designed to operate natively and seamlessly on its respective platform, so that you can consult your data with ease whenever you need it.
Windows
Linux/Ubuntu
MacOS
Complete and unconditional respect for employees’ personal data
EmpMonitor protects your rights, but also those of your employees
Privacy is a very sensitive topic.
As an employer, you have the right to know how your employees are utilizing company resources, including work time and equipment. However, this right should not come at the expense of the relationship of trust that you have with your employees.
That’s why EmpMonitor uses an intelligent process to ensure that the privacy of your employees’ personal data is always respected, and only work-related data is monitored.
EmpMonitor is installed onto a separate, administrative user account that is set up specifically for work. The account that your employee uses for personal purposes is never accessed.
Additionally, in the interest of safeguarding the integrity of the device, EmpMonitor monitors emails for phishing and spam attacks, which could lead to dangerous data leak